Log Aggregation Platform
Logs are invaluable for purposes like monitoring, troubleshooting, and security monitoring. But they may also inadvertently contain sensitive information, including intellectual property (IP), Personal Identifiable Information (PII), or security-sensitive information.
The vast amounts of log data, often from numerous input sources, are another headache for most complex IT environments. The essential information is hidden among a continuous flow of application log output, which can quickly become a huge bottleneck when generating essential reports. In the midst of a ransomware or DDoS attack, any second brings you closer to disaster; real-time insights are essential.
To overcome the sensitive information-related risks, and achieve real-time insights, you should have full data custody, real-time data processing at your fingertips and a clever way to overcome the cloud costs of storing endless log files.
Solution
We developed a secure, scalable, real-time streaming platform where:
Results
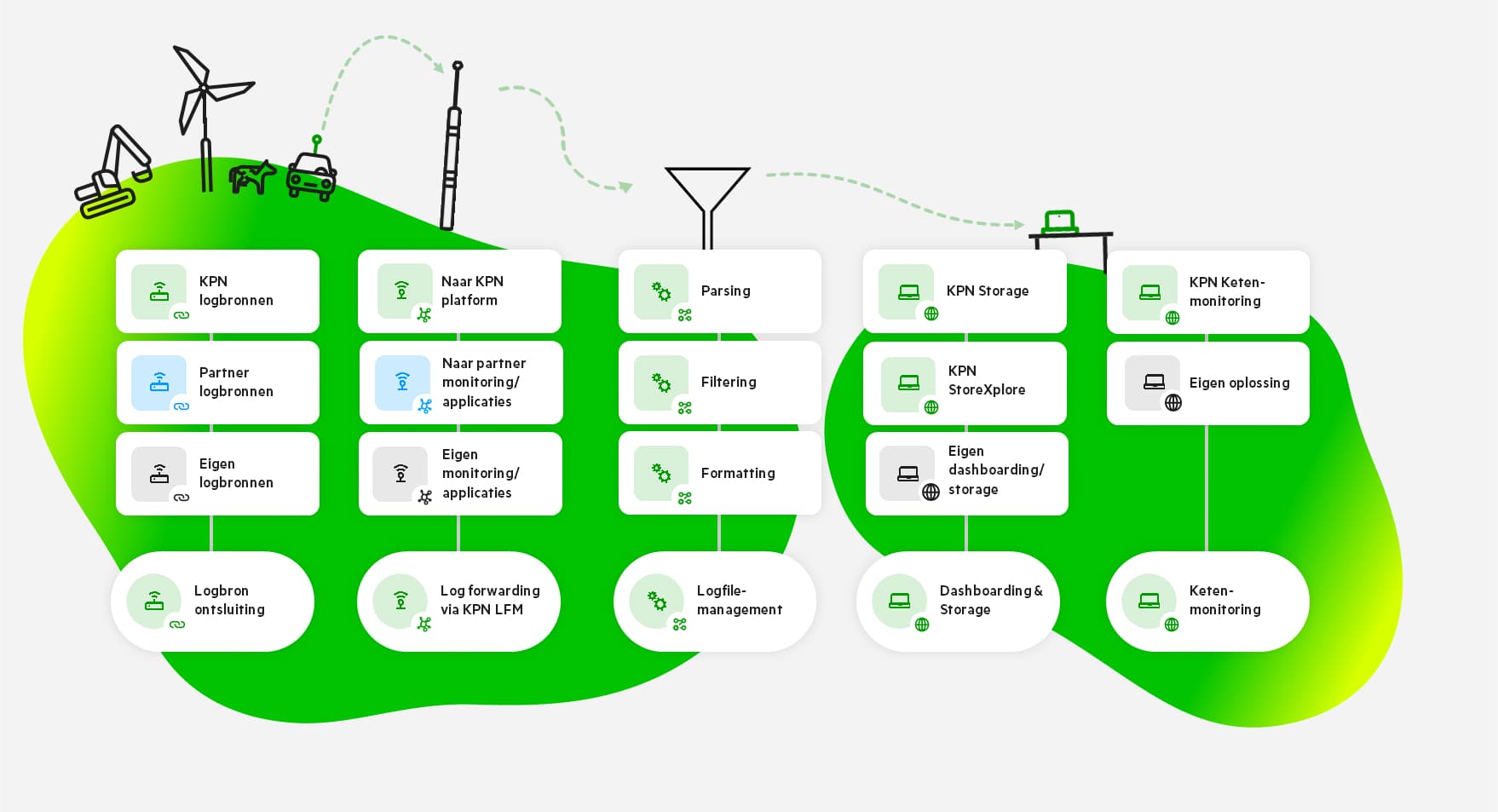
Our secure data platform manages data access, permissions and centralizes all log sources–streamlining the parsing, filtering, formatting, and forwarding of log files. This improved efficiency saves a lot of time and costs. The real-time insights drastically improve incident response and oversight, essential during security breaches.
Behind the scenes
We engineered a cloud native streaming platform for extensive log data source ingestion, enabling on-the-fly analysis and processing for comprehensive monitoring and security incident evaluations. The processed data is then streamed to diverse long-term storage and reporting systems.
The Technology
- Apache Kafka
- Apache Kafka MirrorMaker
- Apache Kafka Proxy
- Kubernetes
- Logstash
The Expertise
- Kafka scaling and optimization
- Data engineering
- Kubernetes security
- Observability (monitoring, logging, distributed tracing)
The Expert
“We faced challenges in quickly processing a lot of data from different sources. Data from multiple logging systems across different platforms needed to be sent reliably and securely. We solved this by implementing numerous secure Kafka proxy endpoints and Logstash where needed. I really enjoyed figuring out how we could ensure minimal disruption and continuous logging during platform upgrades on Kubernetes. It was a satisfying challenge because of its complexity.”
”We faced challenges in quickly processing a lot of data from different sources. It was a satisfying challenge because of its complexity.
Tom BillietSoftware Architect
Join us!
Want to work on similar projects?
Introverts and extroverts, geeks, nerds, and digital poets… Klarrio is the perfect place to learn and teach, experiment and brainstorm, exercise your brain, and feed your passion. Surrounded by people with amazing, world-changing talents.
Contact us!
Control your destiny
Big Data Engineering. Architecture & Data Platform Engineering. Site Reliability Engineering. Consulting. And customized Open Source projects for companies of all sizes. What can Klarrio do for you today?
Other Projects
Just a few projects examples.


